Studying Cybersecurity - How to Learn New Concepts
Learning cybersecurity or any "specialty" within IT can be challenging. Whether you're a Sysadmin, Security Analyst, Network Engineer, or Database Administrator, there's a lot of learning involved. So how do you get started? And what can help you along? There are two concepts that I often find myself coming back to: Black Boxes and Elephants.
Black Boxes - Focusing on What's Important
When I'm learning something I frequently ask why or how. I usually have to ask (and find out) or I have trouble focusing on the actual subject I'm trying to learn. As you can imagine, this can be both a good and bad thing. Go too far down the rabbit hole? You've lost your way and have become distracted. Be inquisitive and learn some of the details behind new concepts? Now you have a deeper understanding of a topic. This is where Black Boxes come in. Try to recognize when you've strayed too far from the original path, mark it for later reading, and let that area function without you understanding what's happening. At least until you've learned what you set out to learn originally.
The good side: Say you're brushing up on your networking knowledge and are learning about VLANs. You can either accept that broadcast messages do not reach nodes on another VLAN despite being connected to the same switch...or you can find out why. This is a great opportunity to learn a bit about Ethernet frames and 802.1Q, Access vs Trunk ports, etc.
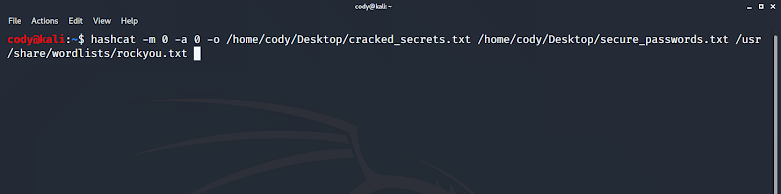
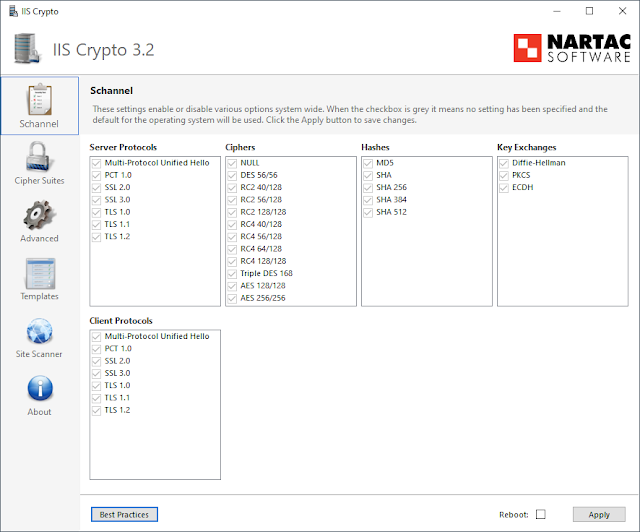
The bad side: Say you're learning some of the finer details of TLS/SSL. Public Key Infrastructure, Certificate Authorities, web browser certificate stores, and the asymmetric vs symmetric encryption steps are all crucial. I've personally placed a Black Box on the mathematical process of how a key can be used to encrypt something but not decrypt it (in the case of asymmetric encryption). There is some very complicated math involved there and I'm willing to trust that the process just works. But everything "before" that? Fair game. Insecurities in SSL, improvements made in TLS 1.3, why SHA-256 hashes should be used in TLS 1.2 and not MD5, and the pros/cons of using ECC vs RSA...all good things to explore because they're actually relevant to what you were originally trying to learn. At least if you ever have to create a certificate and secure traffic to a website.
Knowing where and when to place a Black Box can be extremely helpful and keep you focused. Understand that there is a process that takes place, you're given some output from it that you need, and can carry on with what you're trying to do.



Comments
Post a Comment